
In an ever-evolving digital landscape, the protection of external user accounts has become paramount for organisations across all industries. As cyber threats continue to advance, the implementation of advanced cloud identity management services, such as Azure Active Directory Business-to-Consumer (Azure AD B2C), has emerged as a crucial strategy for safeguarding sensitive data. This detailed case study unfolds the transformative journey of an anonymous client, partnering with the A4S team to fortify authentication security through the deployment of Azure AD B2C Risky Sign-In.
Cybersecurity threats, ranging from sophisticated phishing attacks to ransomware incidents, have underscored the need for robust authentication measures. As businesses increasingly embrace digital transformation, the vulnerabilities associated with external user access become ever more apparent. This case study delves into the strategic decision of the anonymous client to leverage Azure AD B2C Risky Sign-In, exploring the challenges faced, the meticulous solution crafted by the A4S team, and the tangible benefits derived from the enhanced authentication security measures.
Azure AD B2C, while offering robust identity and access management capabilities, poses specific challenges that organisations need to address:

The A4S team engaged in a collaborative effort with the client, conducting a comprehensive risk assessment before implementing Azure AD B2C Risk-Based Sign-In. The solution was tailor-made to address specific risk scenarios identified as critical for the client’s security posture:
“Ever since implementing Entra ID B2C risky sign-in protection, our organisation has benefited from greater levels of security for our external user accounts. The seamless integration and robust features of Entra ID B2C risky sign-in protection have increased our levels of assurance and confidence when keeping client data safe. The security measures embedded in Entra ID B2C have provided us with unparalleled confidence in safeguarding sensitive customer information. The risk-based conditional access policies and continuous monitoring have significantly strengthened our security posture, protecting our users and our brand.”
Azure B2C (Business-to-Consumer) is a cloud identity management solution from Microsoft, designed to provide authentication and authorisation for consumer-facing applications.
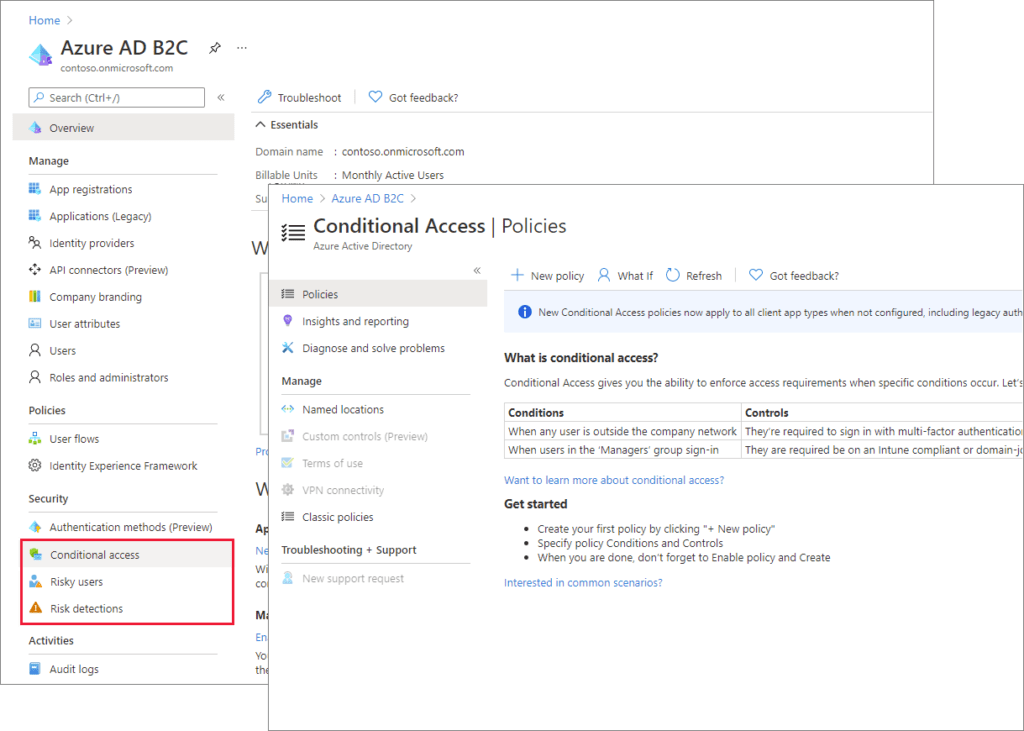
Azure Active Directory B2C enhances security by providing risk-based conditional access, dynamic policy enforcement, and integration with Microsoft Defender ATP to protect against identity threats and unauthorised access.
Azure B2C authentication refers to the process of verifying user identities and granting access to applications through secure, scalable methods, including multi-factor authentication (MFA) and conditional access policies.
Challenges include ensuring legal compliance with data protection laws, balancing user experience with security, selecting appropriate authentication options, and adhering to configuration best practices.
Azure AD B2C Risk-Based Sign-In dynamically assesses sign-in risks based on factors like unusual locations, sign-in times, failed attempts, and device health, prompting additional authentication steps or blocking access as needed.
To see the wide range of projects we’ve worked on, click here to read other case studies.